Connecting the Dots: Why Security Knowledge Integration Matters
Learn how connecting fragmented knowledge silos can transform security in ways that traditional approaches cannot.
· Roman Jasins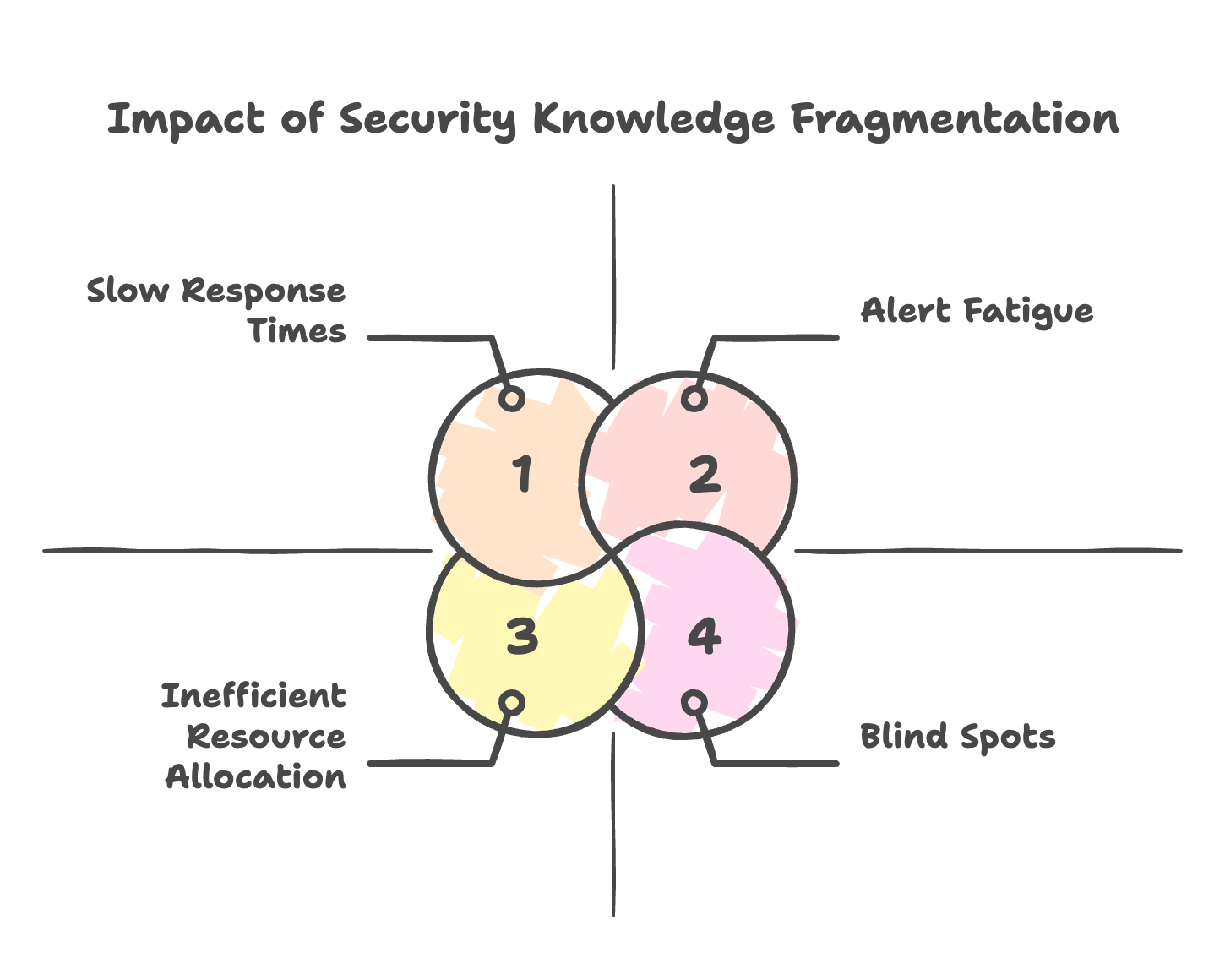
Connecting the Dots
There is a troubling pattern that we have seen in enterprises of all sizes: fragmented security knowledge. And in today’s fast-evolving landscape, this fragmentation is more “dangerous” than ever. Just like the parable of the blind men and the elephant—where each man touches a different part and describes a completely different animal - teams often work with partial views of their security posture, leading to serious blind spots and ineffective decision-making.
This isn’t a technology problem—it’s a knowledge problem. And solving it requires understanding why we got here and how a new approach to security knowledge can transform our effectiveness.
The Fragmentation Dilemma
Ask any CISO about their security stack, and they’ll likely describe a complex ecosystem of specialized tools:
- Vulnerability scanners identifying system weaknesses
- SIEM solutions aggregating logs
- GRC platforms tracking compliance requirements
- Endpoint protection monitoring devices
- Threat intelligence feeds providing external context
- Ticketing systems managing remediation
- Documentation systems housing policies and procedures
Each tool serves a purpose, solving a specific problem. But collectively, they’ve created a new problem: security knowledge silos.
The consequences are significant:
- Blind Spots: Critical relationships between data points remain invisible because they exist in separate systems.
- Alert Fatigue: Without proper context, teams suffer from high volumes of false positives.
- Inefficient Resource Allocation: Teams struggle to prioritize efforts based on real risk.
- Slow Response Times: When incidents occur, piecing together the full picture takes too long.
- Labor-intensive processes: Where this often manifests in the most obvious ways is the compliance burden - meeting regulatory requirements becomes labor-intensive manual work, that you have to repeat over and over.
Knowledge Integration Creates Value
This fragmentation challenge isn’t unique to security. If you’ve ever been through so-called digital transformation projects, you most likely have seen how organizational knowledge is trapped across numerous disconnected platforms—from documentation to analytics to customer data. Each system operates with its own concepts and models, creating “an unnavigable web of knowledge that required a tremendous amount of time and expertise to operate and utilize”.
The solution isn’t to build better individual tools but to fundamentally rethink how knowledge should be connected. When you get this right, the results from unifying and making knowledge more accessible could be truly transformative, and the benefits are wide-ranging, from vendor consolidation to serious productivity gains. More on how we apply this below. Also, there is a pretty good example of that in the recent post of Sebastian Siemiatkowski where he shared insights about their internal transformation.
Why Traditional Approaches Fall Short
Traditional approaches to security information management have attempted to solve this through:
- Data Aggregation: Simply collecting data in one place, but without preserving relationships
- Dashboard Overlays: Creating visualization layers on top of disconnected systems
- API Integrations: Building point-to-point connections between specific tools
- Manual Correlation: Relying on analysts to mentally connect the dots
While these approaches provide some benefit, they don’t address the fundamental knowledge structure problem. They still require significant human effort to make connections, and they break down as scale and complexity increase.
The Graph Paradigm Shift
Although this is not new, one of the most promising solutions to this fragmentation comes from graph databases. Unlike traditional databases that store information in tables or documents, graph databases are purpose-built to manage and query complex relationships.
In a security context, this paradigm shift enables:
- Relationship Mapping: Native representation of how assets, vulnerabilities, threats, controls, and people connect
- Context Preservation: The ability to understand the full context around any security element
- Pattern Recognition: Identification of complex patterns that span across traditional security domains
- Impact Analysis: Quick determination of the true business impact of security issues
- Risk Propagation: Proper modeling of how risk flows through interconnected systems
This isn’t just a technical improvement—it’s a fundamental shift in how we model and interact with security knowledge.
Building a Connected Security Knowledge Foundation
For organizations looking to overcome security knowledge fragmentation, here are key principles to guide your approach:
1. Start with Ontology, Not Tools
Begin by modeling your security domain—what are the key entities and relationships that matter in your security program? This might include:
- Assets and their dependencies
- Threats and vulnerabilities
- Controls and their coverage
- Compliance requirements
- Business processes and their criticality
Your ontology should reflect your business reality, not be dictated by tool limitations.
2. Prioritize Integration Architecture
Rather than treating integrations as an afterthought, make them central to your security architecture:
- Implement a graph database as your knowledge foundation
- Define clear integration patterns for ingesting data
- Establish data transformation processes that preserve relationships
- Create robust data quality and validation mechanisms
3. Balance Automation with Expertise
The most effective security knowledge systems combine:
- Automated data collection and relationship mapping
- Expert input to validate connections and provide context
- AI-assisted analysis to identify patterns and anomalies
- Human judgment for critical decision-making
Neither pure automation nor pure manual effort delivers optimal results—the magic happens at the intersection.
4. Focus on Continuous Learning
Your security knowledge foundation should:
- Evolve as your environment changes
- Incorporate feedback from security operations
- Learn from past incidents and near-misses
- Adapt to new threat patterns and techniques
The goal isn’t a static representation but a dynamic, learning system.
How Wingman Embodies These Principles
At Peak Defence, we’ve built our Wingman (think of it as an AI-first GRC platform) based on these exact principles. Using graph database technology, Wingman creates an intelligent relationship map of your security landscape, revealing connections and patterns that traditional GRC platforms miss.
Our approach combines:
- Graph-powered relationship mapping to eliminate knowledge silos
- AI-driven analytics that leverage these relationships to reduce false positives
- Human expertise through your own security experts or our professional CISO services to provide strategic guidance
Rather than adding another disconnected tool to your security stack, Wingman serves as a unifying layer that connects your security knowledge and enhances your existing investments.
Embracing the Connected Future
Whether you choose to build your own security knowledge foundation or leverage platforms like Wingman, it is important to keep in mind that the future of effective security operations depends on connected knowledge.
In a world of increasing complexity and ever-evolving threats, organizations can no longer afford the limitations of fragmented security information. Just as Klarna discovered in their broader digital transformation, security teams that unify their knowledge will gain tremendous advantages in efficiency, effectiveness, and resilience.
The path forward isn’t about more tools—it’s about better connected knowledge.
If you’d like to learn more about building a connected security knowledge foundation or see how Wingman can help integrate your security information, contact us or drop our team a message at contact[@]peakdefence.com.
Related Topics:
Related Articles
What AI Means for Your Security Team
Explore how AI is transforming security management and empowering security teams...
Read More →Stay Updated
Subscribe to receive the latest security insights, industry trends, and expert advice directly to your inbox.
